Cloud security encompasses a comprehensive set of technologies, policies, and best practices designed to safeguard data, applications, and infrastructure operating within cloud environments. As organizations increasingly depend on cloud platforms to store and process critical information, securing these digital ecosystems has become more important than ever.
In simple terms, cloud computing (often referred to as “the cloud”) delivers computing resources including servers, storage, databases, and software over the internet on an on-demand basis. This enables businesses to grow faster, cut down operational costs, and improve scalability. However, with this flexibility comes the responsibility of protecting sensitive information and maintaining control across complex, multi-cloud or hybrid setups.
The core objectives of cloud security include:
- Data Protection: Safeguarding sensitive information both during transmission and while stored.
- Multi-Cloud Security: Managing and securing data across multiple cloud service providers.
- Access Control: Ensuring only verified users, devices, and applications can access cloud environments.
By adopting strong cloud security frameworks, organizations can fully leverage the benefits of the cloud improved agility, scalability, and innovation while minimizing potential risks and meeting compliance requirements.
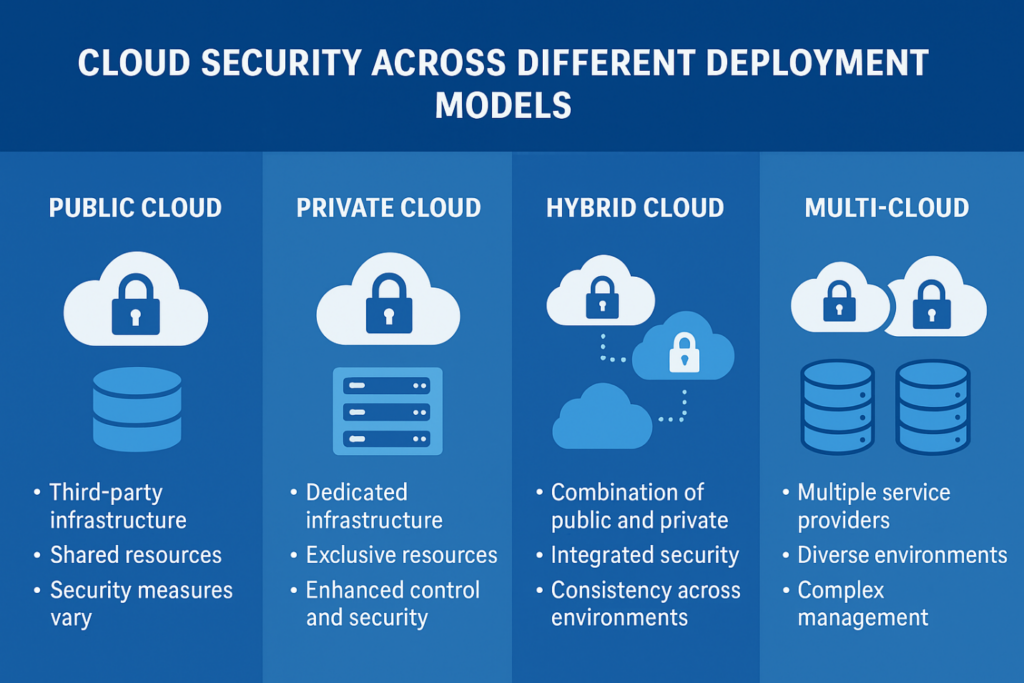
Cloud Security Across Different Deployment Models
Cloud environments can be deployed in various ways public, private, hybrid, and multi-cloud, each offering unique advantages and requiring specific security strategies. Understanding how to secure each model is key to building a reliable cloud security architecture.
Public Cloud
Public clouds, managed by providers like AWS, Microsoft Azure, and Google Cloud, offer cost efficiency and scalability by sharing infrastructure among multiple users.
· Security Concerns: Shared infrastructure can lead to risks like misconfigurations or data breaches.
· Best Practices: Use strong encryption, identity and access management (IAM), and multi-factor authentication (MFA) to protect sensitive data and ensure only authorized access.
Private Cloud
A private cloud serves a single organization, providing maximum control over data, compliance, and security. It’s ideal for industries with strict regulatory requirements such as healthcare and finance.
· Security Concerns: While more secure, private clouds demand higher investment and strong internal management.
· Best Practices: Enforce strict access controls, conduct regular audits, and deploy data loss prevention (DLP) systems to comply with standards like HIPAA and PCI DSS.
Hybrid Cloud
Hybrid cloud setups combine both public and private environments, allowing organizations to balance flexibility and control. For example, public clouds may host customer-facing apps while private clouds store sensitive financial data.
· Security Concerns: Managing consistent security across both environments and securing data transfers between them can be complex.
· Best Practices: Use end-to-end encryption, unified monitoring, and consistent access policies to maintain security and visibility.
Multi-Cloud
A multi-cloud approach utilizes multiple public cloud providers to prevent vendor lock-in and enhance performance.
· Security Concerns: Inconsistent security policies across providers can create gaps and vulnerabilities.
· Best Practices: Adopt centralized security management tools, like Cloud Access Security Brokers (CASBs) and Cloud Infrastructure Entitlement Management (CIEM) platforms, to maintain uniform protection and continuous threat monitoring.
By selecting the right cloud deployment model and implementing these best practices, organizations can achieve the ideal balance between flexibility, control, and compliance ensuring a secure and resilient cloud environment.
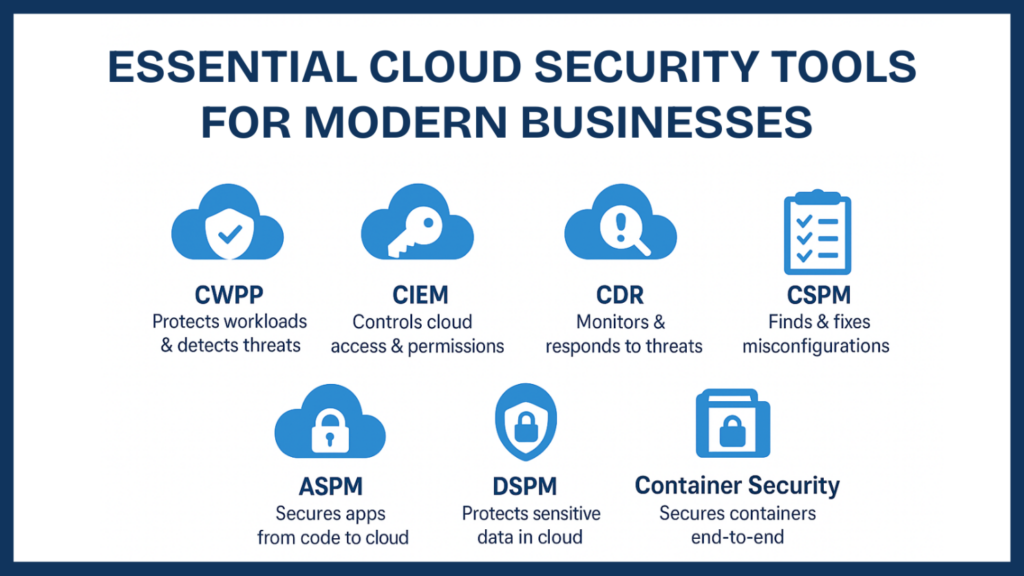
Essential Cloud Security Tools for Modern Businesses
To protect sensitive data and maintain trust in the digital era, organizations are increasingly relying on advanced cloud security tools. These solutions are built to secure data, manage user access, detect vulnerabilities, and respond to threats in real time. A Cloud-Native Application Protection Platform (CNAPP) brings together several of these capabilities under one unified system scanning for risks, monitoring workloads, and securing information from code to cloud.
Here’s an overview of key cloud security tools businesses use to strengthen their defense:
1. Cloud Workload Protection Platforms (CWPPs): CWPPs secure cloud-based workloads, including virtual machines, containers, and serverless functions. They continuously scan for misconfigurations and vulnerabilities, providing real-time threat detection and protection. These tools are vital for companies managing diverse and complex cloud environments.
2. Cloud Infrastructure Entitlement Management (CIEM): CIEM solutions control and monitor user permissions and access levels across cloud systems. By preventing over-privileged accounts, CIEM reduces the risk of unauthorized access and helps maintain strong identity governance in large-scale environments.
3. Cloud Detection and Response (CDR): CDR tools provide real-time monitoring and threat response capabilities within cloud infrastructures. They detect suspicious behavior early and enable quick responses to minimize impact and maintain operational continuity.
4. Cloud Security Posture Management (CSPM): CSPM continuously evaluates your cloud environment for security misconfigurations, compliance gaps, and risks. It’s particularly essential for multi-cloud setups, ensuring that systems remain aligned with industry standards and best practices.
5. Application Security Posture Management (ASPM): ASPM tools safeguard cloud-based applications by analyzing code, dependencies, and configurations to detect vulnerabilities. They are crucial for organizations adopting DevSecOps, ensuring security throughout the software development lifecycle.
6. Data Security Posture Management (DSPM): DSPM focuses exclusively on data protection within cloud environments. It ensures sensitive data such as PII and financial records remains encrypted, properly accessed, and securely managed to comply with privacy regulations.
7. Container Security: With the rise of Docker and Kubernetes, container security tools have become indispensable. They secure the entire container lifecycle from development to deployment by scanning for vulnerabilities and ensuring secure runtime operations.
By integrating these essential cloud security tools, organizations can create a resilient cloud defense strategy that ensures compliance, prevents breaches, and maintains full visibility over their data and systems.

Why Zero Trust Matters in Cloud Security?
Zero Trust is a modern security approach based on the idea that no user, device, or application should be trusted automatically whether it’s operating inside or outside the network. In today’s cloud-driven world, where business data is distributed across multiple platforms and services, this model has become vital for maintaining data integrity and confidentiality.
Core Principles of Zero Trust
· Continuous Verification: Every user, device, and application request is continuously verified before granting access, ensuring that unauthorized entities are immediately blocked.
· Least Privilege Access: Access rights are granted strictly based on necessity, minimizing the potential damage from compromised accounts or systems.
· Micro-Segmentation: Cloud environments are divided into smaller, isolated segments, preventing attackers from moving laterally within the system if they gain access to one area.
In a cloud ecosystem where threats can emerge from both internal and external sources, the Zero Trust model establishes a proactive layer of defense. By constantly validating identities and activities, it reduces the risk of data breaches and unauthorized access.
Ultimately, Zero Trust is essential for modern cloud security, offering real-time protection for users, data, and applications across diverse cloud environments.
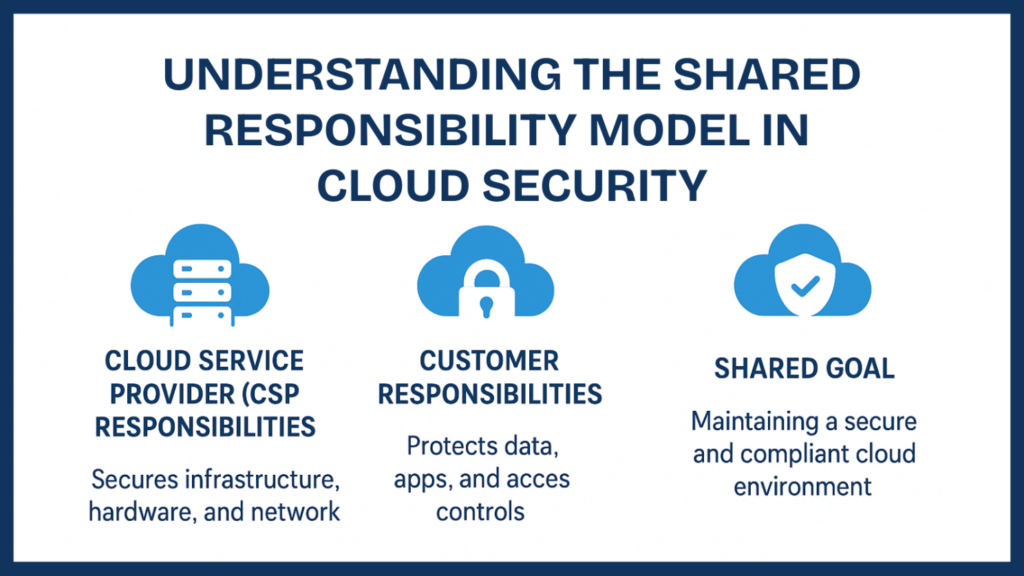
Understanding the Shared Responsibility Model in Cloud Security
The shared responsibility model is a foundational concept in cloud security that clearly defines how security duties are divided between the cloud service provider (CSP) and the customer. It’s an essential framework that ensures both parties play their part in maintaining a secure and compliant cloud environment.
How It Works
The cloud provider is responsible for securing the cloud infrastructure including the hardware, software, network, and data centers that power the cloud. This involves protecting against cyber threats, maintaining uptime, and ensuring that the core platform remains resilient and secure.
The customer, however, is responsible for securing everything within the cloud such as their data, applications, user access, and configurations. This means setting proper access controls, encrypting sensitive information, patching vulnerabilities, and maintaining compliance with relevant regulations.
For instance, while a CSP ensures that the underlying infrastructure is safe, it’s up to the customer to properly manage permissions, monitor configurations, and secure any data or applications they deploy in the cloud.
By clearly understanding and applying the shared responsibility model, organizations can build stronger, more secure cloud environments reducing risk and ensuring accountability at every level.
Cloud Security for Regulated Industries
Industries such as healthcare, finance, and retail operate under strict data protection laws. For these sectors, cloud adoption requires strong security measures to safeguard sensitive information and maintain compliance with industry regulations.
Cloud Security in Healthcare (HIPAA Compliance)
Healthcare providers must comply with HIPAA to protect Protected Health Information (PHI). This includes using encryption, multi-factor authentication, and regular security audits to ensure data privacy. Most healthcare organizations rely on private or hybrid clouds to maintain better control over PHI while staying compliant with HIPAA standards.
Cloud Security in Finance (PCI DSS Compliance)
Financial institutions follow PCI DSS standards to secure payment and transaction data. They use encryption, access control, and network monitoring to protect sensitive financial information. Many financial firms prefer hybrid cloud models, combining scalability with strong data protection and compliance measures.
Cloud Security in Retail (Securing eCommerce)
Retailers must protect customer payment and personal data while complying with PCI DSS. Using public cloud services, they secure eCommerce platforms with encryption, CASBs (Cloud Access Security Brokers), and application firewalls to prevent data breaches and ensure safe online transactions.
By aligning with these compliance frameworks, organizations across regulated industries can confidently use cloud technology while keeping their data protected and operations compliant.

Cloud Security Risks
Understanding cloud security risks is essential for protecting your data and systems. Without identifying potential vulnerabilities, it’s impossible to build a strong defense. Weak cloud security can expose businesses to various cyber threats, both internal and external.
Common Cloud Security Threats:
· Infrastructure Risks: Legacy IT systems and unreliable third-party storage services can cause compatibility issues or service disruptions.
· Internal Threats: Human errors, such as misconfigured access controls or weak authentication, can unintentionally open security gaps.
· External Threats: Cyberattacks like malware, phishing, and DDoS remain major dangers to cloud environments.
Unlike traditional networks, the cloud has no fixed perimeter making insecure APIs and account hijacking significant threats. Hackers often exploit weak credentials to move laterally across connected systems, access sensitive data, or even use cloud servers for storing stolen information.
Additionally, third-party data storage and internet dependency introduce operational risks. Outages whether from network failures or data center power loss can cause downtime or permanent data loss. For this reason, maintaining local data backups and adopting a data-centric security approach are critical to ensuring resilience and continuity.

Inventiv Technology — Your Strategic Ally in Cloud Security
Partnering with Inventiv Technology means aligning your business with a trusted leader in cloud security innovation. We go beyond traditional protection methods our approach combines advanced security frameworks, real-time monitoring, and compliance-driven strategies to ensure your cloud infrastructure is not only secure but also future-ready.
At Inventiv, we understand that every organization has unique operational challenges and risk factors. That’s why our experts design customized cloud security solutions that align perfectly with your business goals, whether you’re running on public, private, or hybrid cloud environments. From identity and access management (IAM) to data encryption, threat detection, and incident response, we deliver end-to-end protection that evolves with your needs.
Our partnership model focuses on transparency, scalability, and continuous improvement. By working closely with your team, we ensure seamless integration of security protocols without disrupting business operations. With Inventiv Technology by your side, you gain more than a service provider you gain a long-term security partner committed to strengthening your digital foundation and helping your business thrive with confidence.

Conclusion
In today’s digital era, cloud security is vital for business continuity and trust. As organizations grow their digital presence, managing data, compliance, and user access across platforms becomes increasingly complex and even a single vulnerability can cause serious damage.
At Inventiv Technology, we help businesses stay protected with intelligent, proactive, and scalable cloud security solutions. Our experts combine advanced tools with deep industry insight to build secure, compliant, and high-performing cloud environments.
Whether it’s healthcare, finance, or eCommerce, Inventiv safeguards your data and strengthens your digital foundation. With us as your trusted partner, you can innovate confidently, scale securely, and thrive in the cloud-first future.
• Visit Us: 🌐 www.inventivtechnology.com
• Email Us on: info@inventivtechnology.com
#CloudSecurity #CyberSecurity #DataProtection #CloudComputing #SecureTheCloud #InfoSec #NetworkSecurity #CloudDefense #SecurityAwareness #DigitalSecurity #CloudCompliance #DataPrivacy #RiskManagement #SecurityCompliance #ZeroTrust #CloudInfrastructure #CloudGovernance #CloudSecurityTrends #ThreatIntelligence #CloudResilience #CyberResilience #SecurityInsights #SecureYourBusiness #CloudSecuritySolutions #EnterpriseSecurity #ProtectYourData #CloudInnovation #SmartSecurity #CloudStrategy
- By ASFARZAIDI
- 8